SAVNET WG Seeks to Improve Existing SAV Mechanisms in Intra-Domain and Inter-Domain Networks
Source address spoofing (IP spoofing) remains a significant challenge for network operators seeking to secure their networks against malicious actors who often use IP spoofing techniques in reflection amplification attacks, which are the major source of large-scale denial of service (DoS) attacks.
Implementing source address validation (SAV) is an important mitigation technique for identifying and rejecting packets with spoofed source IP addresses. Since 2014, The MANRS initiative has been calling on network operators to implement SAV as close to the source as possible. More recently, in 2022, the Internet Engineering Task Force (IETF) formed the Source Address Validation in Intra-domain and Inter-domain Networks Working Group (SAVNET WG) to improve SAV capability in both intra-domain and inter-domain networks.
SAV discussions in the IETF
SAV discussions in the IETF have been going on for more than a decade.
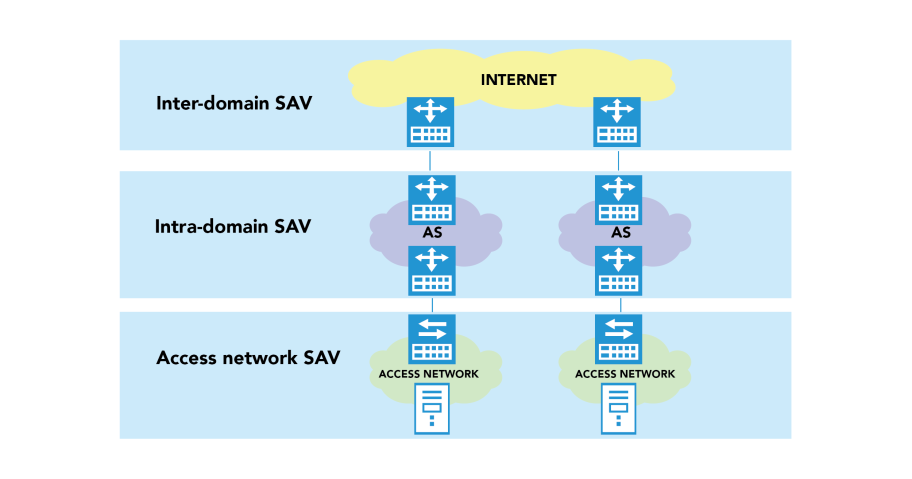
In 2008, source address validation architecture (SAVA) [RFC 5210] was proposed to divide SAV into three different checking levels (Figure 1):
- Access network SAV
- Intra-domain SAV
- Inter-domain SAV
Between 2012 and 2017, the Source Address Validation Improvement Working Group (SAVI WG) published several standards for access network SAV.
Access network SAV is implemented at switches in the access network and prevents each host from using spoofed source addresses. If all switches in the world deployed SAV, there would be no traffic with spoofed source addresses in the Internet and no need to deploy SAV at the intra-domain or inter-domain level. However, given numerous access networks are managed by different operators, it is not practical for global switches to deploy SAV simultaneously.
In cases where access networks cannot deploy SAV, intra-domain and inter-domain SAV can help filter spoofed packets as close to the source as possible.
The current practice for intra-domain and inter-domain SAV is uRPF-related mechanisms (for example., strict uRPF, loose uRPF, feasible uRPF, EFP-uRPF, VRF-mode uRPF) or ACL-based SAV.
As recommended by MANRS Action#2, network operators are encouraged to implement strict uRPF or ACL-based SAV at the intra-domain or inter-domain level.
A network operator should implement a system that enables source address validation for their own infrastructure and end users, and for any Single-Homed Stub Customer Networks. This should include anti-spoofing filtering to prevent packets with an incorrect source IP address from entering or leaving the network.
MANRS Action 2: Prevent traffic with spoofed source IP addresses – Filtering
However, existing uRPF-related mechanisms may improperly permit spoofed traffic or block legitimate traffic in the scenario of routing asymmetry. Further, ACL-based SAV requires frequent manual updates in a dynamic network, which leads to high operational overhead. Therefore, new intra-domain and inter-domain SAV mechanisms with high accuracy and low operational overhead are needed.
Get involved in the discussion
The SAVNET WG was approved in June 2022 and has organized two WG meetings at IETF 114 and IETF 115. Its aim is to improve existing SAV mechanisms in intra-domain and inter-domain networks.
Currently, the Working Group is discussing and summarizing the problems of existing SAV mechanisms and proposing requirements for new mechanisms. The new SAV architectures and related O&M mechanisms will be shared with the community for consideration after the WG has reached a consensus on the problem statement and requirements.
Following the requirements, SAVNET WG will then define the new intra-domain and inter-domain SAV architectures that can automatically generate accurate SAV rules at routers with limited operational overhead. Existing architectures or protocols or mechanisms can be used in the new SAV architectures to achieve better SAV functions.
In addition, the Working Group will come up with a separate mechanism to operate and manage the configurations in the new SAV architectures.
The Working Group welcomes network practitioners with an interest in SAV to join the discussion and plans to closely collaborate with MANRS to promote the SAV’s further deployment in the future.
Dan Li is a professor in the Department of Computer Science and Technology at Tsinghua University.
Leave a Comment